Introducing Hive Account Recovery

Shit happens and you may one day be faced with your account being compromised: your private keys have been leaked or stolen and your account and funds are at risk.
Fortunately, each account on the Hive blockchain is linked to a recovery account that can reset the compromised account owner key, enabling its original owner to update it with a new password and keys.
How is the recovery process working?
- You generate a new password and a set of related private and public key pairs.
- You ask the recovery account to reset your password by providing him with the new public owner key.
- The recovery account initiates the change of your credentials
- You have 24 hours to confirm the change.
This post will not explain in detail how to perform these operations but explain what problem may arise and the solution I propose to remedy it.
For details on how to deal with the recovery process, you can read this excellent post written by @abitcoinskeptic. Although a bit outdated, it remains very educational.
The Recovery Account - A trusted cornerstone
What is the Recovery Account?
The recovery account is another Hive account that is able to initiate the recovery of your account, in case you solicit it after your account has been compromised. For the recovery to be possible, you often need to go through a process. On Steemit, Inc. you need to send them a recent password for your account, used no longer than 30 days ago. More information will be required to determine that you are the rightful owner.
What is the role of the Recovery Account?
The duty of the owner of the recovery account is to make sure whoever is asking for the account recovery is the real owner of the account to be recovered before initiating the account recovery procedure.
What if the Recovery Account does not initiate the recovery process?
You’re fucked! This account is the only one to be able to initiate the recovery process.
As you can see, without the recovery account performing steps 3 of the recovery process, it is impossible to finalize the process of resetting your owner key.
Why would the Recovery Account holder not initiate the recovery process?
There can be lots of reasons for this.
- Its owner might not be able to verify you’re the real owner of the account to be recovered
- Its owner might be not responding (unreachable or even dead)
- Its owner might ransom you to perform the task
- You cheated on the owner with his wife or husband and now he/she takes revenge by refusing to comply.
… and many other reasons.
Joking aside, I think that cases 1 and 2 are the most likely, point 2 is the one with the most risk factor.
Many of the accounts on the Hive blockchain have been created by Steemit, inc and still have @steem as their recovery account. Not sure many of us still trust them as a recovery account.
This is also an issue for accounts that are created by regular users who have claimed account tickets using their unused resource credits and are using them to create accounts for others.
When they create an account using their available tickets, they are set by default as the "recovery account". A responsibility maybe they didn't know they have, didn't ask for and don't want. Some may become inactive over time or will be unreachable when someone needs them to recover their account.
Then there's a problem.
How to mitigate these risks
The choice of your Recovery Account is therefore of paramount importance. You need a trusted but, even more, reliable person who:
- is able to identify you with certainty.
- you can reach anytime in the future.
Changing your recovery account from @steem to @hive.io will not solve our issue. Mainly because hive.io is not a single entity that can be fully "trusted" even if the majority of people who are involved in its development are trustworthy people. It is also not “reliable” because no structure has been put in place to ensure such service and availability 24x7.
This is where Hive Recovery comes in.
Hive Recovery is a service that I have set up to work uninterrupted and is completely autonomous.
Navigate to https://tools.hivechain.app/recovery
It’s a very simple webpage where you can securely define @hive.recovery has your recovery account and secure your (future) recovery process.
A - How to configure the recovery account?
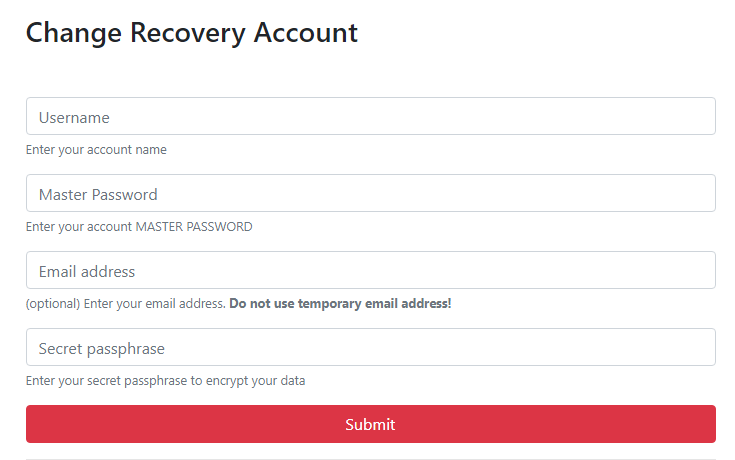
Fill the form with:
- your username (without the
@) - your Master Password (read below why it is asked for)
- your email address. This is optional but will add more security to the recovery process (more on this later in this post)
- a secret passphrase that you and only you will know (a very cool online passphrase generator can be found here)
Once ready, click on the Submit button
At this step of the process, the web page will encrypt your account name and email address (if provided) using your passphrase (let’s call the result of this encryption E1).
The web page will then
- encrypt the E1 once more using both your memo key and @hive.recovery memo key and insert it in the memo of a micro-transfer
- change your recovery account to @hive.recovery
Both operations are performed atomically, which means that if one of the operations fails, neither of them is recorded on the blockchain.
Confirm the broadcasting of the operations and you’re done.
You will need it later if you ever need to recover your account!
After setting up your @hive.recovery as your recovery account, you have to wait 30 days before @hive.recovery will become your recovery account and before you can initiate a recovery. This is to ensure that someone gaining access to your account cannot update the recovery info to his/her own advantage then initiate the recovery process and lock you out.
Why do you need my Master Password?
You Master Password is used to retrieve
- your private owner key: this key is mandatory to issue the
change_recovery_accountoperation to the blockchain. One bird two stones, it will also be used to send the (micro)transfer operation. - your private memo key: this key will be used to encrypt the memo of the above-mentioned transfer.
Your Master Password or Private Keys will NOT been stored or sent over the internet by the Account Recovery Setup process!
B - How to recover my account?
You can only initiate a request to recover your account at least 30 days after performing the previous step since it is only from this moment that @hive.recoverywill officially be your recovery account.
So, let's say your account has been unfortunately compromised and it’s now time to recover it.
Navigate to https://tools.hivechain.app/recovery and go to the second part of the page
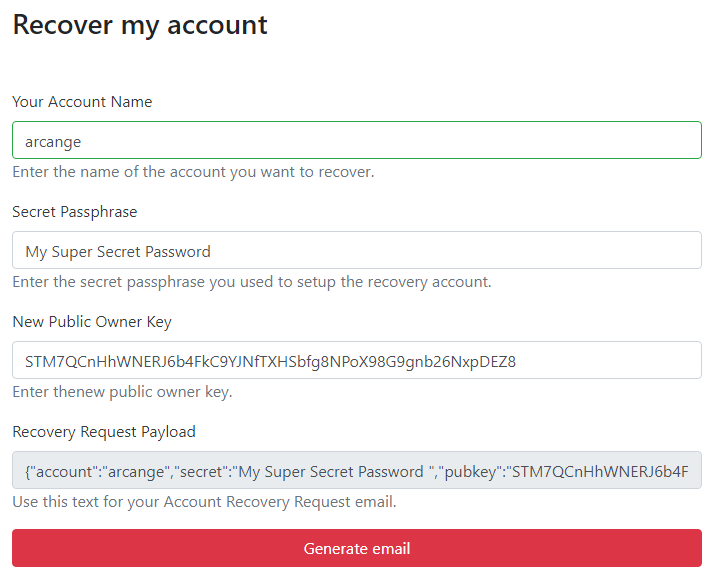
Fill the form with:
- Your username (without the
@) - The secret passphrase you have used to configure your recovery account (step A).
- The public owner key from a new password and keys set you previously generated for your account (more on this below)
Then click on the “Generate Email” button. This will trigger your default email client to create a new email ready to send with pre-filled “to”, “subject” and “body”.
If your email client does not open, you can send an email manually to recovery[at]hivechain.app and copy the Recovery Request Payload text in the body of your email. The subject doesn’t matter. You can put what you want there.
WARNING: If you provided an email address to your memo when setting up the recovery account, you must send the email from the same email address!
When receiving your email, @hive.recovery will parse this payload and:
- verify it is the recovery account of the provided account
- search for the micro-transfer with the encrypted memo
- verify it can decrypt the memo using the provided passphrase
- verify if the account name in the email matches the account name in the decrypted memo
- if an email address has been provided at step A, verify if the email address used to send the payload is the same as the email address in the decrypted memo.
If all these tests pass through, @hive.recovery will then initiate the recovery procedure using the new public owner key
The last thing you will need to do is confirm the recovery request within 24 hours.
How secure is this service?
Considering your account is safe when doing step A, you are the only one to be able to make the micro-transfer using your active key and encrypt information using your memo key. If a hacker changes your password, your keys will change too. This way, @hive.recovery can identify you with certainty.
Also, remember that a double encryption process is used:
- encryption of your data using your passphrase -> E1
- encryption of E1 using memo keys -> E2
With this double encryption process in place, only you and @hive.encrypted can access E2 and read E1, but @hive.encrypted cannot decrypt E1 because it has not your passphrase. No one, including @hive.recovery, can ever read the content of E1 until you provide the passphrase to decrypt it.
Even if a malicious actor finds your passphrase, he/she won’t be able to access E1 because he/she will need your private memo key to decrypt E2 first.
An attacker would need you to get your passphrase AND your memo key (AND optionally your email address and its control) to be able to lock you out of the recovery process.
On the other hand, if these are safe and if @hive.recovery can decrypt E1 and the information it contains matches your data, then it can identify you with certainty and safely initiate the recovery process for you.
A bit about privacy
The only private element that you communicate to @hive.recovery (and therefore to me) is an email address. For obvious reasons, this email address cannot be temporary. We can therefore consider that you could potentially be identified with this email address.
However, remember that this information is encrypted using your passphrase. So no one who does not have this passphrase has access to it. This is also the case for @hive.recovery and me, who will only be able to access it from the moment you initiate a recovery procedure
For the most paranoid of you who still would not trust me, which is perfectly acceptable, you can freely not use this option. It is only provided to add an additional level of security.
Make your own research
The webpage is hosted on https://tools.hivechain.app/recovery
Do not run it from an untrusted website
Exercise due diligence (you should not trust me 😉).
Source code available on Github. You can download and run it locally.
UPDATE:
Several people have rightly pointed out to me that the Hive Keychain extension doesn't work when the webpage is not hosted on a remote server. Therefore, I decided to remove the Hive Keychain integration so that it can now be run entirely locally and without having to use a third party.
The good news is that it will also solve the issue of people who felt left out because they use Hivesigner.
The only drawback is that you must now enter sensitive data. Therefore, please be cautious and double-check where you are running the page from and, if possible, audit the code you are running.
Support
Support for this service is provided on Hivechain.app server on Discord. Use the dedicated Account Recovery dedicated channel.
Hey very cool @arcange
Though I did want to clarify something for readers.
Account recovery CAN NEVER WORK if you do not have a previous working Owner key. This is how the recovery process works.
The recovery account is unable to take over your account at will due to the fact that they need a working owner key to process the account recovery.
@someguy123 has a little more details and technical info about the process https://peakd.com/steem/@someguy123/how-the-steem-account-recovery-works-and-why-your-trustee-can-t-steal-your-account
If you get your password stolen or hacked and someone changes your accounts owner key, you can use the hacked owner key to take back control of your account.
If you lose your password altogether, you are screwed.
YOU CAN NOT RECOVER AN ACCOUNT IF YOU LOSE YOUR PASSWORDS AND DO NOT HAVE ANY BACKUPS FROM PREVIOUS PASSWORDS
(PS: it is up to your recovery account to ask for whatever info they want to verify you are the rightful account owner. This is why it's usually good to have some trusted user or friend act as recovery)
Thank you for the clarification @netuoso.
Everything you mention is indeed explained in the @abitcoinskeptic's post I am referring to. There is a lot to say about the recovery process, but I made the decision not to make this post too long.
I'm preparing en exhaustive account recovery manual that will be published under @hive.recovery account.
Just mainly wanted to clarify the fact that you, in your post, said you can recover accounts if you lose the keys.
That's a slippery slope and many users won't understand or even take time to read any other post about it.
You are right. I removed it from the post to avoid confusion.
Hello, to clarify, you can only recover a changed password for 30 days. So an old password cannot assist you if the password changed more than 30 days ago.
Good point
Suggestion: Should this be clickable and redirect user to Hive Keychain Installation guide or Download link
Keychain has not yet be approved by Google. Hence why I didn't include an install link.
You will find a quick guide on how to do it here
Excellent work!
And what a coincident!! I am also writing a post about my recovery tool https://github.com/codebull/HiveAccountRecovery/ :)
Your tool is indeed really cool and helpful to perform the recovery process.
This post is mainly about providing a secure and reliable "trustee" service.
We should work on merging both.
If you are interested, feel free to contact me on Discord or Telegram
I actually saw your post first :)
I wrote this comment in the middle of writing that post. :D
I appreciate your work but this service is still dependant on your existence!
We are all dependent on the existence of our recovery account.
First, I guess my computer will survive me. The only "weak" point is the server running the small portion of code used to initiate the recovery process. It can run on a very small VPS instance and I can pre-pay for it for the next century.
Second, anyone can change its recovery account at any moment, should he/she learns I'm no more of this world or I or my service is no more trusted.
The strong point of this service is to provide an automated and reliable "identity" verification process.
This said, my plan for the future is to "decentralize" it and integrate it into the hive.io infrastructure.
I changed my recover account 😀 thanks for your tutorial post about recover account change.
Thank you @diamond-head
I appreciate this, but can somebody also please do a tutorial on how to change the recovery account to an alt of yourself (including how to create and alt for yourself with an account creation token) and pin it in the HIVE discord?
Of course this requires keeping both passwords in two different safe locations, but this way you can recover your account by yourself, no third party or complex process needed.
Does steemworld work to change your HIVE recovery account? I guess not.
While steemit was a nice 3rd party to trust for your account recovery, the best is now to set 'null' and simply not lose your key.
Don't trust anyone.
So many questions on this...
It was my understanding that the <30 day old owner key was actually required by base layer consensus to perform recovery.
No?
Also, if someone has stolen your account and changed your keys, doesn't that mean they already know your old memo key? Can't you generate the memo key with the owner key?
I guess I'm still not understanding how the recovery account is unable to steal the account.
Yes, you need a password or private owner key that was valid less than 30 days ago to confirm the request_account_recovery initiated bu the trustee.
No, you need the password to regenerate keys
Because
But,
One more reason to carefully choose your recovery account.
Thank you for the shout out. I may update for peakd, but developments are happening too fast for comfort.
Please remind people, lost passwords can only be recovered if the change happened less than 30 days ago and the user has a password that was valid within the last 30 days. So if it is lost, usually the user is out of luck, unless they just changed it.
You're welcome @abitcoinskeptic
Yeah, things going so fast now on Hive. Hard to catch up 😅
"you must have the latest version of the Hive Keychain extension installed"
What about users who don't want to or can't involve another 3rd party service?
This post has been updated.
The webpage is now fully autonomous and no more rely on third-party apps.
Thank you for the update, and I appreciate you notifying me to check it out.
You're welcome @drutter
Realy great work.. Thankx for news
Thank you @anandjadhao
Thank you for this info
Great tool thank you!
Thanks for this! Will reblock this so I can do this later.
Thank you for this post. I will share it with people who search for this information! 😎
Thank you @manncpt
good service , any idea why am i getting this error ? hive keychain not found i have downloaded it.
Keychain integration has been removed and this post has been updated.
Please re-read the content of this post.
thanks :) just changed mine
Nice, keep your account #safu for the next 30 days 😉
Thanks for doing great workon this blockchain man! I really appreciate we get to have this stuff
Thank you @bigtakosensei
Excellent work. I already had a very bad experience when my account was hacked about a month ago. I hope it doesn't happen to me again. I really enjoyed reading this work. I appreciate the information and your dedication to keeping each user safe. Thank you very much.
Right. Bookmarked and thank you for trying to keep us all safe!
Blessings!
You're welcome @papilloncharity
hi!
any chance to see Steempress on Hive?
I'm not a SteemPress developer. Better to ask @howo of @Fredrikaa 😉
Meant Steem reply omg, my bad))
SteemReply has been replaced by Engage.
Click on the small image in this comment (right side) to read more about it
@arcange👍👍👍👍 wow so cool! ty!
btw your witness now fully supported by @infa 🙂
Thank you for your unfailing support @rollie1212, really appreciated!
@arcange😉
Is the account recovery process the only way to change your account keys (posting, active and memo)? I have already set a new account password but I cannot seem to find a way to change these keys?
If you have set a new master password, then all your keys have changed!
Thank you so much for this info. I spent hours yesterday trying to figure this out.
can you do more coding example repos like the claim accounts with RC? Like I want to add hive signer, key chain etc etc to Memehub, so some solid update to date code examples that cover the nuance thatll likely trip up a noob would be killer :)
👋Hi @arcange,
Good news! We've added Hive Account Recovery to the
Hive Blockchain Directory, here:
https://hivewhat.com/directory/hive-account-recovery/
Swarm!
Thank you @hivewhat
Book marked thank you for this definitely going to look into this tomorrow. Great write up my friend. Have a good one.
Btw.
What if I have lost both my owner/master keys over 30 days ago, but I have all the other keys, and a trusted recovery account. Is it still possible to change the master password?
I'm kind of in a pickle right now, because that's exactly what happened, and I couldn't use the recovery account option for the 30 day transition period from @steemit to the other recovery account. And now the recovery services tell me the passwords haven't been changed in the last 30 days.Scratch that, it appears that I still had a copy of the owner key, but since I had given it an obscure name I couldn't see it. (Thank goodness I found it. I was already sweating.)
But I now know this scenario could happen again. Maybe we should have some way to recover forgotten (and not stolen) passwords too.
There is absolutely no way to recover a forgotten or lost password.
That's why it is so important not to lose it. No password, no account recovery!
@argange
As usual, thank you for your work. I'm returning back to Hive after COVID-19, Stay-at-home, and other insanities are calming down. I'm transferring my Steem funds to HIVE. I changed my HIVE keys and now I need to finish changing my recovery account from Steem.
I tried utilizing your form to begin the account recovery change, but I see an unfilled red rectangle above the user name entry block. Can you please tell me what that means?
Thank you very much.
Hi @arcange - thinking of using Hive Recovery Service but just wanted to check it's still fully supported and you plan to keep it running for the foreseeable future as this article is quite old now?
Thanks for all the great work as always!
Hey, the Hive Recovery service is still operational and will continue to be maintained.